bossからtls1.3勉強しといてと言われたのでちょっと触ってみました。
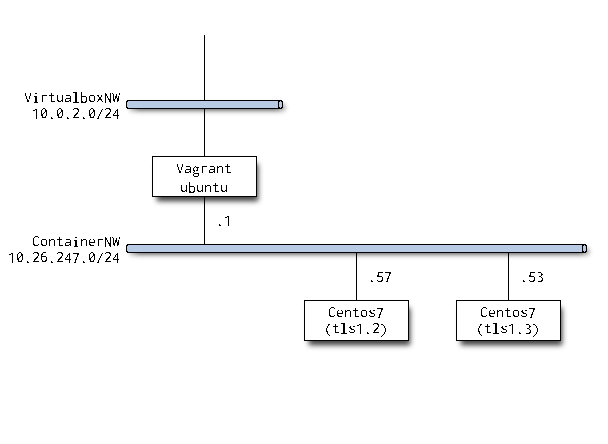
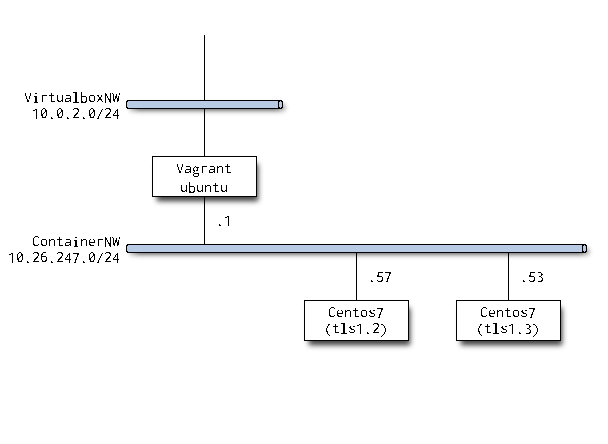
環境
自宅環境のVMにコンテナでtls1.2と1.3のサーバを立てました。
コンテナにしたのは構築に失敗したら壊してすぐ作り直せるようにです。
サーバは基本デフォルトのパラメータです。
詳細は後日書こうと思います。
vagrant@ubuntu-bionic:~$ cat /etc/lsb-release
DISTRIB_ID=Ubuntu
DISTRIB_RELEASE=18.04
DISTRIB_CODENAME=bionic
DISTRIB_DESCRIPTION="Ubuntu 18.04.4 LTS"
vagrant@ubuntu-bionic:~$
vagrant@ubuntu-bionic:~$ lxc --version
3.0.3
vagrant@ubuntu-bionic:~$ sudo lxc list
+--------+---------+---------------------+-----------------------------------------------+------------+-----------+
| NAME | STATE | IPV4 | IPV6 | TYPE | SNAPSHOTS |
+--------+---------+---------------------+-----------------------------------------------+------------+-----------+
| tls1-2 | RUNNING | 10.26.247.57 (eth0) | fd42:a221:114c:4ccf:216:3eff:fe28:3f6e (eth0) | PERSISTENT | 0 |
+--------+---------+---------------------+-----------------------------------------------+------------+-----------+
| tls1-3 | RUNNING | 10.26.247.53 (eth0) | fd42:a221:114c:4ccf:216:3eff:fec7:2a5e (eth0) | PERSISTENT | 0 |
+--------+---------+---------------------+-----------------------------------------------+------------+-----------+
tls1.2と1.3の違い
アルゴリズムとかハンドシェイクとかガラッと変わったようです。
RFCは読めていないので細かいところは参考サイトを参照ください。
www.wolfssl.jp
products.nvc.co.jp
Server Hello以降は暗号化というところだけ覚えましたw
実際にアウトプットを見よう
ホストから各コンテナへの通信を見てみます。
curlで叩いてみます。
パケットフロー
ホストでtcpdumpを仕掛けてcurlの結果を取りました。
後学のためにローカルPCに持ってきてWireshekで確認します。
といってもフローだけなんでtsharkで確認します。
ホストもサービスも名前引き無効にしてあります。
よく見るTLSのフローですね。
PS C:\Users\masashi\tools\vagrant\ubuntu> & 'C:\Program Files\Wireshark\tshark.exe' -t ad -r .\tls1-2.pcap
1 2020-02-27 22:44:32.511597 10.26.247.1 → 10.26.247.57 TCP 74 41712 → 443 [SYN] Seq=0 Win=64240 Len=0 MSS=1460 SACK_PERM=1 TSval=2750354114 TSecr=0 WS=128
2 2020-02-27 22:44:32.511637 10.26.247.57 → 10.26.247.1 TCP 74 443 → 41712 [SYN, ACK] Seq=0 Ack=1 Win=65160 Len=0 MSS=1460 SACK_PERM=1 TSval=2630713681 TSecr=2750354114 WS=128
3 2020-02-27 22:44:32.511676 10.26.247.1 → 10.26.247.57 TCP 66 41712 → 443 [ACK] Seq=1 Ack=1 Win=64256 Len=0 TSval=2750354114 TSecr=2630713681
4 2020-02-27 22:44:32.514209 10.26.247.1 → 10.26.247.57 TLSv1 305 Client Hello
5 2020-02-27 22:44:32.514223 10.26.247.57 → 10.26.247.1 TCP 66 443 → 41712 [ACK] Seq=1 Ack=240 Win=65024 Len=0 TSval=2630713684 TSecr=2750354117
6 2020-02-27 22:44:32.515992 10.26.247.57 → 10.26.247.1 TLSv1.2 1508 Server Hello, Certificate, Server Key Exchange, Server Hello Done
7 2020-02-27 22:44:32.516031 10.26.247.1 → 10.26.247.57 TCP 66 41712 → 443 [ACK] Seq=240 Ack=1443 Win=62848 Len=0 TSval=2750354118 TSecr=2630713685
8 2020-02-27 22:44:32.517143 10.26.247.1 → 10.26.247.57 TLSv1.2 192 Client Key Exchange, Change Cipher Spec, Encrypted Handshake Message
9 2020-02-27 22:44:32.517521 10.26.247.57 → 10.26.247.1 TLSv1.2 117 Change Cipher Spec, Encrypted Handshake Message
10 2020-02-27 22:44:32.517726 10.26.247.1 → 10.26.247.57 TLSv1.2 178 Application Data
11 2020-02-27 22:44:32.517852 10.26.247.57 → 10.26.247.1 TLSv1.2 333 Application Data
12 2020-02-27 22:44:32.524781 10.26.247.1 → 10.26.247.57 TLSv1.2 97 Encrypted Alert
13 2020-02-27 22:44:32.524884 10.26.247.57 → 10.26.247.1 TCP 66 443 → 41712 [FIN, ACK] Seq=1761 Ack=509 Win=65024 Len=0 TSval=2630713694 TSecr=2750354127
14 2020-02-27 22:44:32.524994 10.26.247.1 → 10.26.247.57 TCP 66 41712 → 443 [FIN, ACK] Seq=509 Ack=1762 Win=64128 Len=0 TSval=2750354127 TSecr=2630713694
15 2020-02-27 22:44:32.525005 10.26.247.57 → 10.26.247.1 TCP 66 443 → 41712 [ACK] Seq=1762 Ack=510 Win=65024 Len=0 TSval=2630713694 TSecr=2750354127
6行目、Chenge Cipher SpecのあとからApplication Dataになってます。
なるほど、確かに早いフェーズで暗号化されているようですね。
PS C:\Users\masashi\tools\vagrant\ubuntu> & 'C:\Program Files\Wireshark\tshark.exe' -t ad -r .\tls1-3.pcap
1 2020-02-27 22:44:59.110859 10.26.247.1 → 10.26.247.53 TCP 74 44406 → 443 [SYN] Seq=0 Win=64240 Len=0 MSS=1460 SACK_PERM=1 TSval=2995470197 TSecr=0 WS=128
2 2020-02-27 22:44:59.110903 10.26.247.53 → 10.26.247.1 TCP 74 443 → 44406 [SYN, ACK] Seq=0 Ack=1 Win=65160 Len=0 MSS=1460 SACK_PERM=1 TSval=1922381237 TSecr=2995470197 WS=128
3 2020-02-27 22:44:59.110951 10.26.247.1 → 10.26.247.53 TCP 66 44406 → 443 [ACK] Seq=1 Ack=1 Win=64256 Len=0 TSval=2995470197 TSecr=1922381237
4 2020-02-27 22:44:59.115120 10.26.247.1 → 10.26.247.53 TLSv1 326 Client Hello
5 2020-02-27 22:44:59.115146 10.26.247.53 → 10.26.247.1 TCP 66 443 → 44406 [ACK] Seq=1 Ack=261 Win=65024 Len=0 TSval=1922381242 TSecr=2995470201
6 2020-02-27 22:44:59.116893 10.26.247.53 → 10.26.247.1 TLSv1.3 1608 Server Hello, Change Cipher Spec, Application Data, Application Data, Application Data, Application Data
7 2020-02-27 22:44:59.116907 10.26.247.1 → 10.26.247.53 TCP 66 44406 → 443 [ACK] Seq=261 Ack=1543 Win=64128 Len=0 TSval=2995470203 TSecr=1922381243
8 2020-02-27 22:44:59.118206 10.26.247.1 → 10.26.247.53 TLSv1.3 146 Change Cipher Spec, Application Data
9 2020-02-27 22:44:59.118409 10.26.247.1 → 10.26.247.53 TLSv1.3 171 Application Data
10 2020-02-27 22:44:59.118552 10.26.247.53 → 10.26.247.1 TLSv1.3 369 Application Data
11 2020-02-27 22:44:59.118705 10.26.247.53 → 10.26.247.1 TLSv1.3 369 Application Data
12 2020-02-27 22:44:59.118776 10.26.247.1 → 10.26.247.53 TCP 66 44406 → 443 [ACK] Seq=446 Ack=2149 Win=64128 Len=0 TSval=2995470205 TSecr=1922381245
13 2020-02-27 22:44:59.118871 10.26.247.53 → 10.26.247.1 TLSv1.3 326 Application Data
14 2020-02-27 22:44:59.119097 10.26.247.1 → 10.26.247.53 TLSv1.3 90 Application Data
15 2020-02-27 22:44:59.119181 10.26.247.1 → 10.26.247.53 TCP 66 44406 → 443 [FIN, ACK] Seq=470 Ack=2409 Win=64128 Len=0 TSval=2995470206 TSecr=1922381245
16 2020-02-27 22:44:59.135002 10.26.247.1 → 10.26.247.53 TCP 66 [TCP Retransmission] 44406 → 443 [FIN, ACK] Seq=470 Ack=2409 Win=64128 Len=0 TSval=2995470221 TSecr=1922381245
17 2020-02-27 22:44:59.135160 10.26.247.53 → 10.26.247.1 TCP 78 443 → 44406 [ACK] Seq=2409 Ack=471 Win=64896 Len=0 TSval=1922381262 TSecr=2995470205 SLE=470 SRE=471
18 2020-02-27 22:44:59.185832 10.26.247.53 → 10.26.247.1 TCP 66 443 → 44406 [FIN, ACK] Seq=2409 Ack=471 Win=64896 Len=0 TSval=1922381312 TSecr=2995470205
19 2020-02-27 22:44:59.185904 10.26.247.1 → 10.26.247.53 TCP 66 44406 → 443 [ACK] Seq=471 Ack=2410 Win=64128 Len=0 TSval=2995470272 TSecr=1922381312
コンテンツはデフォルトページしか置いてないのでHEADで確認します。
一応-vで詳細も。
ちゃんとCA局も作ったのでCA証明書も読み込みます。
自己証明書ちゃんとSubject書いたので一応住所等隠します。
ちょっと長くなるのでサーバからHEADが返るまでを抽出します。
vagrant@ubuntu-bionic:~$ curl -I -v -s --cacert cacert.pem https://tls1-2.vagrant.lab --tlsv1.2
* Rebuilt URL to: https://tls1-2.vagrant.lab/
* Trying 10.26.247.57...
* TCP_NODELAY set
* Connected to tls1-2.vagrant.lab (10.26.247.57) port 443 (
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: cacert.pem
CApath: /etc/ssl/certs
* TLSv1.2 (OUT), TLS handshake, Client hello (1):
* TLSv1.2 (IN), TLS handshake, Server hello (2):
* TLSv1.2 (IN), TLS handshake, Certificate (11):
* TLSv1.2 (IN), TLS handshake, Server key exchange (12):
* TLSv1.2 (IN), TLS handshake, Server finished (14):
* TLSv1.2 (OUT), TLS handshake, Client key exchange (16):
* TLSv1.2 (OUT), TLS change cipher, Client hello (1):
* TLSv1.2 (OUT), TLS handshake, Finished (20):
* TLSv1.2 (IN), TLS handshake, Finished (20):
* SSL connection using TLSv1.2 / ECDHE-RSA-AES256-GCM-SHA384
* ALPN, server accepted to use http/1.1
* Server certificate:
* subject: C=JP; ST=XXXX; L=XXXX-Shi; O=XXXX; OU=labo; CN=tls1-2.vagrant.lab
* start date: Feb 23 09:49:06 2020 GMT
* expire date: Feb 22 09:49:06 2021 GMT
* common name: tls1-2.vagrant.lab (matched)
* issuer: C=JP; ST=XXXX; O=XXXX; OU=labo; CN=masashi.lab
* SSL certificate verify ok.
> HEAD / HTTP/1.1
> Host: tls1-2.vagrant.lab
> User-Agent: curl/7.58.0
> Accept: */*
>
< HTTP/1.1 200 OK
opensslコマンドでも出力ががっつり違います。
vagrant@ubuntu-bionic:~$ curl -I -v -s --cacert cacert.pem https://tls1-3.vagrant.lab --tlsv1.3
* Rebuilt URL to: https://tls1-3.vagrant.lab/
* Trying 10.26.247.53...
* TCP_NODELAY set
* Connected to tls1-3.vagrant.lab (10.26.247.53) port 443 (
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: cacert.pem
CApath: /etc/ssl/certs
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Unknown (8):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Client hello (1):
* TLSv1.3 (OUT), TLS Unknown, Certificate Status (22):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN, server accepted to use http/1.1
* Server certificate:
* subject: C=JP; ST=XXXX; L=XXXX-Shi; O=XXXX; OU=labo; CN=tls1-3.vagrant.lab
* start date: Feb 24 07:40:57 2020 GMT
* expire date: Feb 23 07:40:57 2021 GMT
* common name: tls1-3.vagrant.lab (matched)
* issuer: C=JP; ST=XXXX; O=XXXX; OU=labo; CN=masashi.lab
* SSL certificate verify ok.
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
> HEAD / HTTP/1.1
> Host: tls1-3.vagrant.lab
> User-Agent: curl/7.58.0
> Accept: */*
>
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS Unknown, Unknown (23):
< HTTP/1.1 200 OK
openssl
opensslでも動きを見てみます。
これも長いので証明書の出力が終わってからセッションチケットの前まで切り出します。
見てみるとは言いましたが、久しぶりにTLS周り触ったのでここまでくるともう語れません…
vagrant@ubuntu-bionic:~$ openssl s_client -connect tls1-2.vagrant.lab:443 < /dev/null
…
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA
Server Temp Key: ECDH, P-256, 256 bits
---
SSL handshake has read 1657 bytes and written 446 bytes
Verification error: unable to verify the first certificate
---
New, TLSv1.2, Cipher is ECDHE-RSA-AES256-GCM-SHA384
Server public key is 2048 bit
Secure Renegotiation IS supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:
Protocol : TLSv1.2
Cipher : ECDHE-RSA-AES256-GCM-SHA384
Session-ID: 19240C3640E7DA207845593E7E385F87FD52D11704BDED285BEBAD1A617CAC71
Session-ID-ctx:
Master-Key: 57637D21DB43586B74829F55977F0712F46E9D17DB804271535CBE9AF3D55C4FF5252A1AADD5B625FA6FF9B5085CF9C2
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 300 (seconds)
TLS session ticket:
…
vagrant@ubuntu-bionic:~$ openssl s_client -connect tls1-3.vagrant.lab:443 < /dev/null
…
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA-PSS
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 1527 bytes and written 400 bytes
Verification error: unable to verify the first certificate
---
New, TLSv1.3, Cipher is TLS_AES_256_GCM_SHA384
Server public key is 2048 bit
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
Early data was not sent
Verify return code: 21 (unable to verify the first certificate)
---
---
Post-Handshake New Session Ticket arrived:
SSL-Session:
Protocol : TLSv1.3
Cipher : TLS_AES_256_GCM_SHA384
Session-ID: 6F61CBF0B3482E50F00FD12E49E8A8CFA0ECC699B82F3256D97410EDBC0E5EDA
Session-ID-ctx:
Resumption PSK: BE63E7454914EC023103C2F3C6E6B41B8294D23A5A4C15B2866F706839D93E428B41D99AEAAEED930BFC9C97B6C47870
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 300 (seconds)
TLS session ticket:
…
結論
フローはわかったが詳細がよくわかりません!
セキュリティの世界は広くて深い魔界の分野の認識ですが、
本件についてもパケットのフローを見るだけで精一杯でした。
本当は仕様アルゴリズムの詳細とか0-RTTの動きとかまで見て記事書けたらと考えていたんですが、
とてもじゃないですが永遠に公開できないと思ったので
恥ずかしながらいったん結果のみ書くだけにしておきます。
先ほどの参考サイト・RFCを読み込まないといけませんが、
その前に暗号化入門読み直しですね。
(第3版まだ見てないし)
悔しいので本件は調べなおしてリベンジしたいですね。